Privacy and Security Issues in Data Mining and Machine Learning: International ECML/PKDD Workshop, PSDML 2010, Barcelona, Spain, September 24, 2010. Revised Selected Papers | SpringerLink
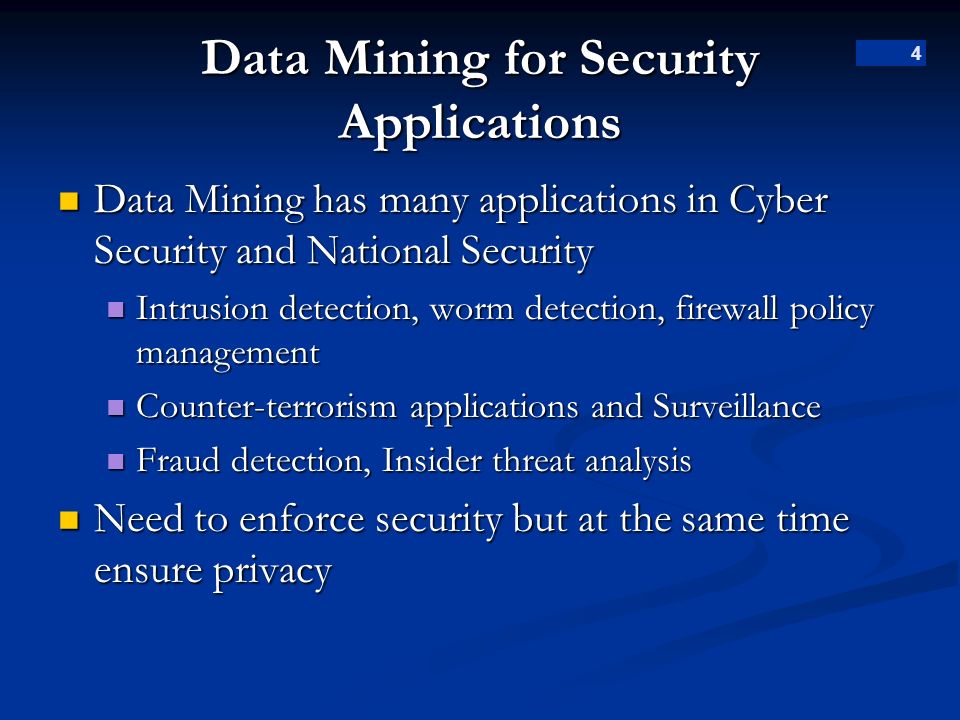
1 Data Mining for Surveillance Applications Suspicious Event Detection Dr. Bhavani Thuraisingham April ppt download

Emerging Technologies in Data Mining and Information Security: Proceedings of IEMIS 2018, Volume 1 | SpringerLink

Applications of Data Mining in Computer Security (Advances in Information Security, 6): Barbará, Daniel, Jajodia, Sushil: 9781402070549: Amazon.com: Books

Graph Data Mining: Algorithm, Security and Application (Big Data Management): Xuan, Qi, Ruan, Zhongyuan, Min, Yong: 9789811626081: Amazon.com: Books










![PDF] A Study on Data Mining Frameworks in Cyber Security | Semantic Scholar PDF] A Study on Data Mining Frameworks in Cyber Security | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/b095b4625733f8521439e54db09bed2b9970a808/3-Figure1-1.png)